
Zero Trust Security or ZTNA is a technology trend on the rise, widely adopted by companies to enhance IT security. This technology concept emphasizes that nothing behind the firewall is inherently secure. Therefore, it is imperative to verify requests originating from open networks.
Zero Trust Security advises users not to trust any request, regardless of its origin and source. Users must verify before accessing any information or resources.
Furthermore, this article will delve deeper into what Zero Trust Security is and how to provide the best Zero Trust Security solution to help businesses optimize their security.
What is Zero Trust Security?

Zero Trust Security is an IT security method that enforces strict identity verification for every person and device attempting to access resources on a network, regardless of their location within or outside the network perimeter.
In other words, this cybersecurity approach doesn’t establish trust in the system but rather eradicates it. This strategy aims to safeguard modern environments and facilitate digital transformation through robust authentication methods, network segmentation, prevention of lateral movement, and the provision of seven layers of cybersecurity.
Benefits and How Zero Trust Security Works to Protect Businesses ?
Zero Trust Security is presented as a more effective model compared to the traditional perimeter or safe zone-based approach, which has been the foundational concept for securing company assets.
The traditional model gives businesses the impression of two zones: the external zone, perceived as a dangerous area rife with cyber threats, and the internal zone or safe zone, presumed to be secure and highly trusted. Ironically, most cyberattacks originate from internal zones, which were long thought to be the safest but are, in reality, more vulnerable than external ones. This is often due to employees’ limited knowledge of data security or malicious intent in stealing crucial company information.
Hence, companies require protection like Zero Trust Security, which is modern and adaptable to increasingly complex IT environments. Zero Trust Security not only bolsters IT infrastructure security but also safeguards employees, applications, and data, regardless of their location.
Examples of Using Zero Trust for Companies
Zero Trust is an effective method for enhancing the security of cloud environments, especially given the multitude of clouds, endpoints, and data in modern IT environments. It also enhances visibility from the administrator level to the Chief Information Security Officer (CISO). Additionally, here are some examples of its application in business.
Reducing Business Risks
Mitigate business risks by ensuring that each application and service can only send or access data only after verifying employee identity, including authentication and authorization requirements. This approach allows continuous monitoring of the applications or services in use.
Access Control over Cloud and Containers
Establish access control over clouds and containers by implementing security policies based on workload identity when sending or accessing data. In this context, the security system can be positioned as close as possible to the assets requiring protection, without being affected by network configurations such as IP addresses, ports, and protocols.
How to Implement Zero Trust Security in Your Business Organization
When implementing Zero Trust Security in your business, the first step is to define strategies such as “what to protect” and “necessary protection systems.” Once the strategy is defined, the next step is to select the technology or solution that can support your strategy. One viable solution is Zscaler Zero Trust Exchange.
You can begin by implementing this solution incrementally, starting with securing the most critical assets and progressively covering less critical ones. Zscaler Zero Trust Exchange solutions can deliver immediate benefits by reducing risks and enhancing security control within your business’s cloud environment.
Why is Zscaler the Best Solution for Getting Started with Zero Trust Security?
Zscaler is the top choice for cybersecurity solutions because it is the only vendor that offers a Zero Trust platform specifically designed for the cloud. Additionally, Zscaler consistently receives recognition as a trusted leader in the cybersecurity industry.
source zscaler.com
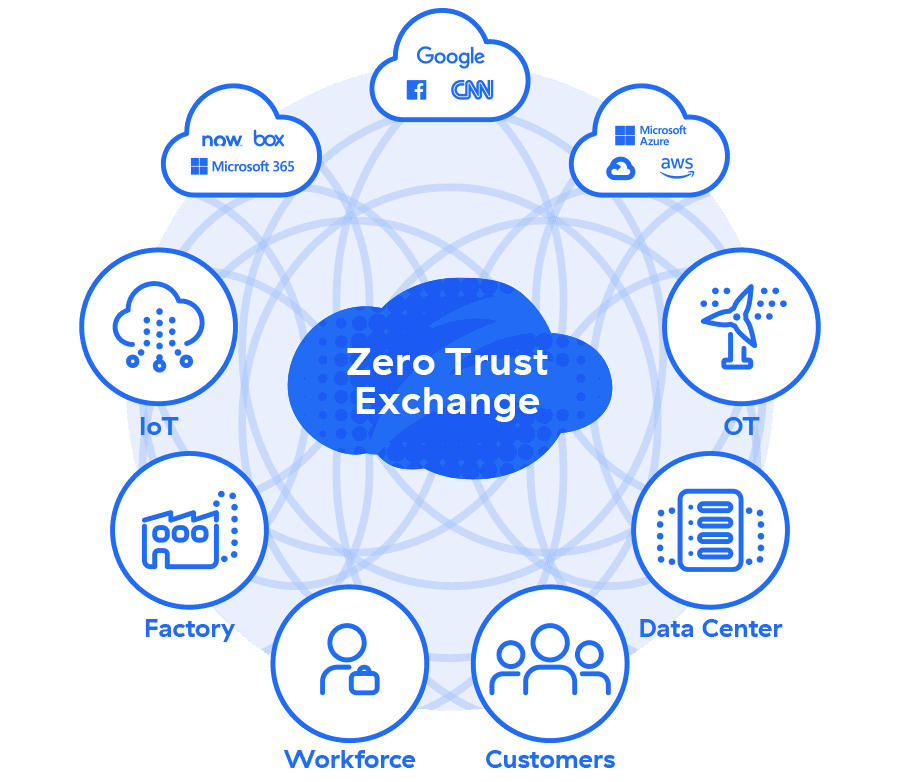
With its flagship platform, Zero Trust Exchange, Zscaler provides a security system to enhance corporate network security. The Zscaler Zero Trust Exchange solution operates by integrating advanced security technologies, including firewalls, web security, and Cloud Access Security Broker (CASB), into one cloud-accessible solution.
Moreover, Zscaler Zero Trust Exchange has also adopted the “Zscaler Zero Trust Network Access” (ZTNA) approach, enabling secure access to any application from any device without the need for a VPN. In fact, this solution includes security features such as risk detection recognition and advanced threat analysis.
Zscaler Zero Trust Exchange offers comprehensive security, an exceptional user experience, and boasts 150 data centers worldwide. With the Zscaler solution, your company can effectively initiate a Zero Trust Security approach, featuring integrated advanced security technology and a guaranteed level of trust.
Read More: Effective Tips to Prevent Downtime in IT Applications and Infrastructure with AIOps
It’s Time to Adopt the Zscaler Zero Trust Exchange Solution at CDT
Central Data Technology (CDT) has now officially partnered with Zscaler. Zscaler’s solutions, particularly Zero Trust Exchange, can be directly obtained through CDT. For further information on implementing the Zscaler Zero Trust Exchange solution in your business, please do not hesitate to contact us by clicking the following link.
Author: Ary Adianto
Content Writers, CTI Group

